ID-Pal CTO and Co-Founder, Rob O’Farrell | What is Identity Verification Series
In the first four articles of this series (Current Techniques in Identity Verification: Establishing a Chain of Trust (continued)) we outlined the current methods of identity verification. Now we must look towards the horizon. As with any technological evolution, new threats emerge, requiring us to adapt and innovate. As the technology moves forward, though, so do our new opportunities.
State of the art fraud
Accepting that physical ID documents are with us for the foreseeable future, let’s take a look at modern techniques in identity fraud.
Camera Injection Attacks and AI-generated Forgeries
While liveness tests establish real-time presence of an individual or document, camera injection attacks present a loophole. Attackers using pre-recorded videos or even AI-generated images can sometimes deceive these systems. Additionally, with advancements in AI, we are witnessing the rise of hyper-realistic images and deepfakes, further challenging our verification systems.
This has given rise to a new generation of defences for identity verification services: Injection Attack Detection. This is a set of techniques used to ensure that images are captured with a real camera, and not just uploaded. This makes it exponentially more difficult for attackers to leverage the power of AI-generated fakes. Particularly when combined with other new defences discussed here.
Physical Document Presence
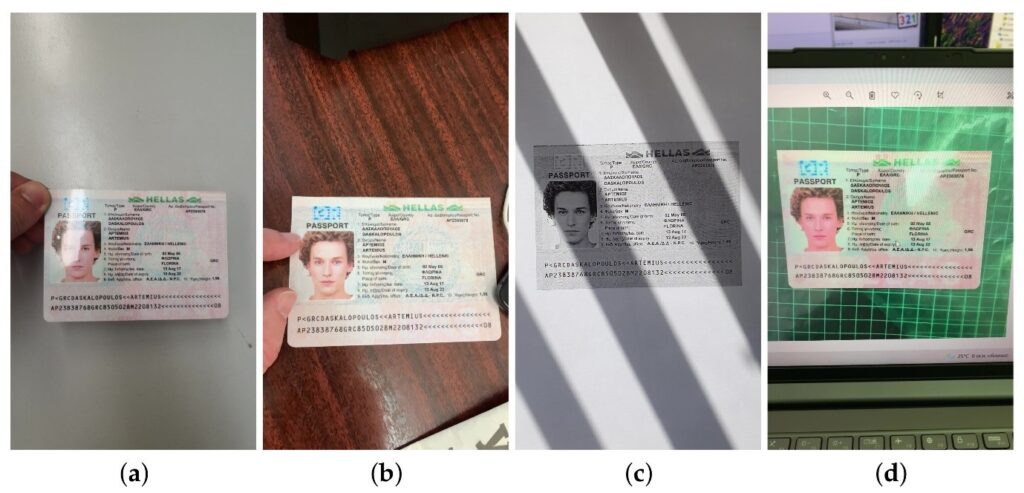
There’s a growing need to verify not just the authenticity of a document, but its physical presence during verification. When an identity document is stolen, attackers often attempt to make modifications to the document so that they can claim ownership of the identity. These changes can be made digitally or physically. To help reduce the risk of digital forgery or tampering, we use Physical Document Presence tests. Cutting-edge tests can detect a print-out, photocopy or simply taking a picture of picture on a screen (known as screen recapture).
Photo Substitution
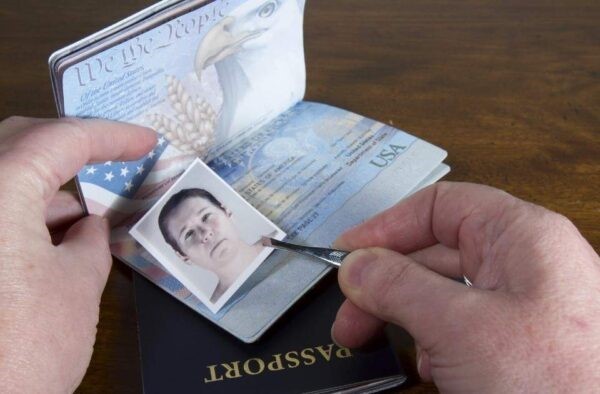
The most valuable modification that a fraudster can make to an ID document is to change the photograph on it. This is known as photo substitution. It can be done with digital manipulation, or by simply laying a cutout of a passport photo over the existing picture? Sound too simple to be true? I suggest taking a look back at the second article in this series (Computerized Trust: How Machines Establish Our Identity). Computers don’t see the world the same way we do so the identity industry has struggled more than you might expect to solve this problem. Thankfully many providers have good solutions now.
Future threats and opportunities
While keeping one eye on the present, we must always keep one eye on the future. With this comes some exciting opportunities, as well as threats we’re all working hard on today.
Post-Quantum Cryptography
Wow, what a mouthful… Let’s try and make that simple. Quantum computers are a new type of computer that are in development utilising the physics of very, very small things. They are incredibly difficult to build, and although there have been promising tests, it’s likely several years until they will become a reality.
If they do become commonplace, we already know they will be good at certain types of problems, like being able to read messages encrypted using current standards. Fraudsters are already gathering messages we all send today so that one day they will be able to quickly decrypt them all. That will likely be the largest exposure of data we’ve ever seen. This is why we cannot rely on “something you know” and it will make the identity verification industry more important than ever.
Thankfully, the world security community is already hard at work designing new ways to encrypt data that quantum computers won’t be able to read.
The Advent of Digital ID Documents
Physical IDs are slowly giving way to digital counterparts. Though convenient, this presents its own set of challenges. How do we verify the authenticity of a digital document as rigorously as a physical one? Drastically different standards of Electronic Identity Documents (eIDs) have been rolled out in different jurisdictions. Schemes rolled out to the standards of the European Regulation on EU Digital Identity Wallets will allow us to verify the ongoing validity of a document against a government database, as well as confirming the ongoing rights affirmed by those documents e.g. the right to drive a vehicle. There are many challenges yet to be resolved in rolling out such schemes on a world-wide scale but that would form an entire series in its own right. Perhaps one for the future.
Self-Sovereign Identity
This is a personal favourite of mine. In a nutshell: this is one approach to creating a world where you are the owner of your own identity data. You decide who gets to see what data. You get to see who still has your data and why. I love the idea of people owning their own data. This will enable you to capture your data once, and share it easily and securely in seconds.
Conclusion
From understanding the essence of trust in human interactions to the sophisticated techniques of the digital age and the emerging challenges on the horizon, our journey through identity verification has been both enlightening and intricate. At its core, whether faced with age-old dilemmas or futuristic challenges, the essence remains unchanged: Trust.
As we navigate this evolving landscape, our commitment remains the same – to ensure simple, secure and convenient identity verification while adapting to, and overcoming, every challenge thrown our way.
Connect with Rob on LinkedIn



